A distributed denial-of-service (DDoS) attack is a malicious attempt to disrupt the normal traffic of a targeted server, service, or network by overwhelming the target or its surrounding infrastructure with a flood of Internet traffic.
DDoS attacks achieve effectiveness by utilising multiple compromised computer systems as sources of attack traffic. Exploited machines can include computers and other networked resources such as IoT devices.
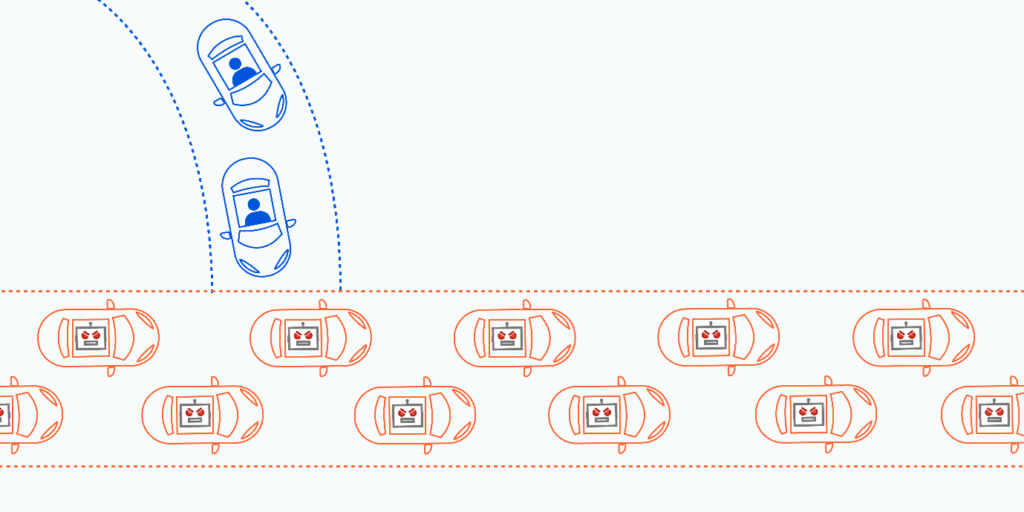
From a high level, a DDoS attack is like an unexpected traffic jam clogging up the highway, preventing regular traffic from arriving at its destination.
How does a DDoS Attack Work?
DDoS attacks are carried out with networks of Internet-connected machines.
These networks consist of computers and other devices (such as IoT devices) which have been infected with malware, allowing them to be controlled remotely by an attacker. These individual devices are referred to as bots (or zombies), and a group of bots is called a botnet.
Once a botnet has been established, the attacker is able to direct an attack by sending remote instructions to each bot.
When a victim’s server or network is targeted by the botnet, each bot sends requests to the target’s IP address, potentially causing the server or network to become overwhelmed, resulting in a denial-of-service to normal traffic.
Because each bot is a legitimate Internet device, separating the attack traffic from normal traffic can be difficult.
How to Identify a DDoS Attack
The most obvious symptom of a DDoS attack is a site or service suddenly becoming slow or unavailable. But since a number of causes — such a legitimate spike in traffic — can create similar performance issues, further investigation is usually required. Traffic analytics tools can help you spot some of these telltale signs of a DDoS attack:
- Suspicious amounts of traffic originating from a single IP address or IP range
- A flood of traffic from users who share a single behavioural profile, such as device type, geolocation, or web browser version.
- An unexplained surge in requests to a single page or endpoint
- Odd traffic patterns such as spikes at odd hours of the day or patterns that appear to be unnatural (e.g. a spike every 10 minutes).
There are other, more specific signs of DDoS attack that can vary depending on the type of attack.
How to Stop DDoS attacks in 3 stages
When under siege from a distributed denial of service (DDoS) attack, systems grind to a halt and often become entirely unresponsive. To stop the attack, defenders must move quickly and navigate three broad response stages:
Stage I: Block the DDoS Attack:
Take immediate steps to attempt to block the attack, which may require outside assistance or even shutting down the resource.
Stage II: Determine the Type of DDoS Attack:
Examine and analyse log files, alerts, and other records for clues regarding source and type of DDoS attack — in some cases, this step may also need to be completed to block the attack.
Stage III: Recover from the DDoS Attack:
Change security architecture, processes, or tools to recover from the current attack and prevent further attacks.
If you have concerns about the security or redundancy of your website, contact our team today.




